Michael Howard, one of the creators of Microsoft's mandatory
Security Development Lifecyle and author of 'Writing Secure Code', has a new book on sofware security.
"The 19 Deadly Sins of Software Security" is a collaboration between Howard, David LeBlanc and John Viega.
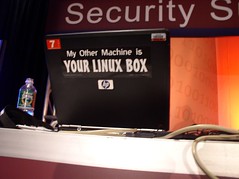
The book, which will debut at
Black Hat USA 2005 briefings later this month, is carved up into 19 chapters:
# Buffer Overflows
# Format String problems
# SQL injection
# Command injection
# Failure to handle errors
# Cross-site scripting
# Failing to protect network traffic
# Use of "magic" URLs and hidden forms
# Improper use of SSL
# Use of weak password-based systems
# Failing to store and protect data
# Information leakage
# Improper file access
# Integer range errors
# Trusting network address information
# Signal race conditions
# Unauthenticated key exchange
# Failing to use cryptographically strong random numbers
# Poor usability
Michael's blog
has an announcement with more information. I'll look for a copy at Black Hat.